 | ||
Alice and Bob are fictional characters commonly used in cryptology, as well as science and engineering literature. The Alice and Bob characters were invented by Ron Rivest, Adi Shamir, and Leonard Adleman in their 1978 paper "A method for obtaining digital signatures and public-key cryptosystems." Subsequently, they have become common archetypes in many scientific and engineering fields, such as quantum cryptography, game theory and physics. As the use of Alice and Bob became more popular, additional characters were added, each with a particular meaning.
Contents
Overview
Alice and Bob are the names of fictional characters used for convenience and to aid comprehension. For example, "How can Bob send a private message M to Alice in a public-key cryptosystem?" is believed to be easier to describe and understand than "How can B send a private message M to A in a public-key cryptosystem?"
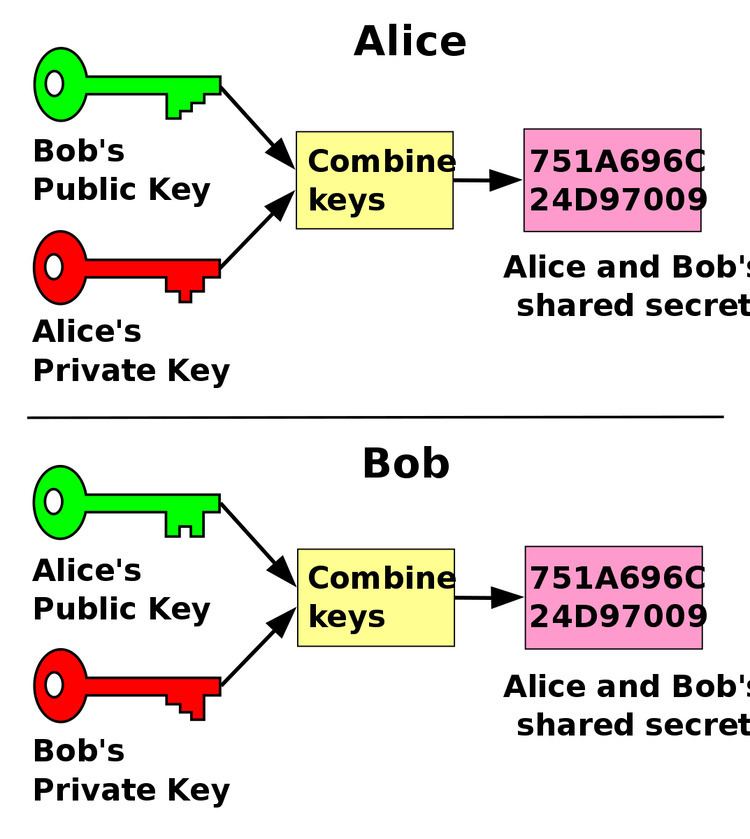
In cryptography and computer security, Alice and Bob are used extensively as participants in discussions about cryptographic protocols or systems. The names are conventional, and often use a rhyming mnemonic.
History
The first mention of Alice and Bob in the context of cryptography was in Rivest, Shamir, and Adleman's article, "A method for obtaining digital signatures and public-key cryptosystems." They wrote, "For our scenarios we suppose that A and B (also known as Alice and Bob) are two users of a public-key cryptosystem" (p. 121). Previous to this article, cryptographers typically referred to message senders and receivers as A and B, or other simple symbols. In fact, in the two previous articles by Rivest, Shamir, and Adleman, introducing the RSA cryptosystem, there is no mention of Alice and Bob.
Within a few years, however, reference to Alice and Bob in cryptological literature became a common trope. Cryptographers would often begin their academic papers with reference to Alice and Bob. For instance, Tal Rabin begun his 1981 paper, "Bob and Alice each have a secret, SB and SA, respectively, which they want to exchange." Early on, Alice and Bob were starting to appear in other domains, such as in Manuel Blum's 1981 article, "Coin Flipping by Telephone: A Protocol for Solving Impossible Problems," which begins, "Alice and Bob want to flip a coin by telephone."
Although Alice and Bob were invented with no reference to their personality, authors soon began adding colorful descriptions. In 1983, Blum invented a backstory about a troubled relationship between Alice and Bob, writing, "Alice and Bob, recently divorced, mutually distrustful, still do business together. They live on opposite coasts, communicate mainly by telephone, and use their computers to transact business over the telephone." In 1984, John Gordon delivered his famous "After Dinner Speech" about Alice and Bob, which he imagines to be the first "definitive biography of Alice and Bob."
In addition to adding backstories and personalities to Alice and Bob, authors soon added other characters, with their own personalities. The first to be added was Eve, the "eavesdropper." Eve was invented in 1988 by Charles Bennet, Gilles Brassard, and Jean-Marc Robert, in their paper, "Privacy Amplification by Public Discussion." In Bruce Schneier's book Applied Cryptography, other characters are listed.
Cast of characters
The most common characters are Alice and Bob. Eve, Mallory, and Trent are also common names, and have fairly well-established "personalities" (or functions). The names often use rhyming mnemonics (for example, Eve, "eavesdropper;" Mallory, "malicious"). Other names are much less common, and flexible in use.
For interactive proof systems there are other characters:
