Digest sizes arbitrary | Speed 6.1 cpb on Core 2. | |
 | ||
Rounds 72 (256 & 512 block size), 80 (1024 block size) | ||
Skein is a cryptographic hash function and one of five finalists in the NIST hash function competition. Entered as a candidate to become the SHA-3 standard, the successor of SHA-1 and SHA-2, it ultimately lost to NIST hash candidate Keccak.
Contents
The name Skein refers to how the Skein function intertwines the input, similar to a skein of yarn.
History
Skein was created by Bruce Schneier, Niels Ferguson, Stefan Lucks, Doug Whiting, Mihir Bellare, Tadayoshi Kohno, Jon Callas and Jesse Walker.
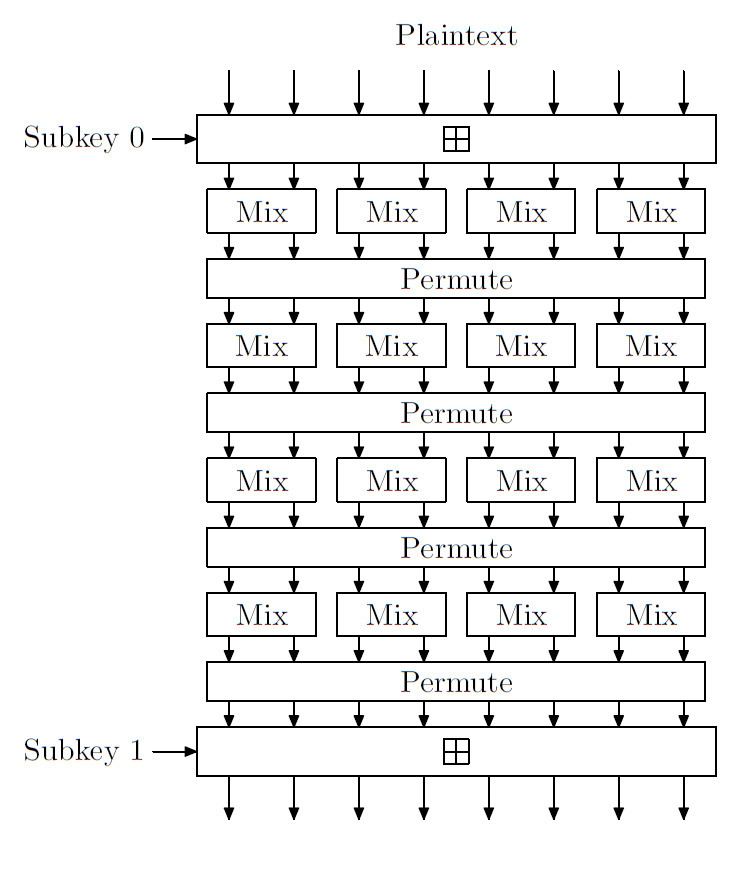
Skein is based on the Threefish tweakable block cipher compressed using Unique Block Iteration (UBI) chaining mode while leveraging an optional low-overhead argument-system for flexibility.
Skein's algorithm as also reference implementation was given to public domain.
Functionality
Skein supports internal state sizes of 256, 512 and 1024 bits, and arbitrary output sizes.
The authors claim 6.1 cycles per byte for any output size on an Intel Core 2 Duo in 64-bit mode.
The core of Threefish is based on a MIX function that transforms 2 64-bit words using a single addition, rotation by a constant and XOR. The UBI chaining mode combines an input chaining value with an arbitrary length input string and produces a fixed size output.
Threefish's nonlinearity comes entirely from the combination of addition operations and exclusive-ORs; it does not use S-boxes. The function is optimized for 64-bit processors, and the Skein paper defines optional features such as randomized hashing, parallelizable tree hashing, a stream cipher, personalization, and a key derivation function.
Cryptanalysis
In October 2010, an attack that combines rotational cryptanalysis with the rebound attack was published. The attack finds rotational collisions for 53 of 72 rounds in Threefish-256, and 57 of 72 rounds in Threefish-512. It also affects the Skein hash function. This is a follow-up to the earlier attack published in February, which breaks 39 and 42 rounds respectively.
The Skein team tweaked the key schedule constant for round 3 of the NIST hash function competition, to make this attack less effective, even though they believe the hash would still be secure without these tweaks.
Examples of Skein hashes
Hash values of empty string.
Skein-256-256("")0x c8877087da56e072870daa843f176e9453115929094c3a40c463a196c29bf7baSkein-512-256("")0x 39ccc4554a8b31853b9de7a1fe638a24cce6b35a55f2431009e18780335d2621Skein-512-512("")0x bc5b4c50925519c290cc634277ae3d6257212395cba733bbad37a4af0fa06af41fca7903d06564fea7a2d3730dbdb80c1f85562dfcc070334ea4d1d9e72cba7aEven a small change in the message will (with overwhelming probability) result in a mostly different hash, due to the avalanche effect. For example, adding a period to the end of the sentence:
Skein-512-256("The quick brown fox jumps over the lazy dog")0x b3250457e05d3060b1a4bbc1428bc75a3f525ca389aeab96cfa34638d96e492aSkein-512-256("The quick brown fox jumps over the lazy dog.")0x 41e829d7fca71c7d7154ed8fc8a069f274dd664ae0ed29d365d919f4e575eebbSkein-512-512("The quick brown fox jumps over the lazy dog")0x 94c2ae036dba8783d0b3f7d6cc111ff810702f5c77707999be7e1c9486ff238a7044de734293147359b4ac7e1d09cd247c351d69826b78dcddd951f0ef912713Skein-512-512("The quick brown fox jumps over the lazy dog.")0x 658223cb3d69b5e76e3588ca63feffba0dc2ead38a95d0650564f2a39da8e83fbb42c9d6ad9e03fbfde8a25a880357d457dbd6f74cbcb5e728979577dbce5436