Original author(s) Development status Active | Repository github.com/nmap/nmap | |
 | ||
Initial release September 1997; 19 years ago (1997-09) Stable release 7.40 / 20 December 2016; 3 months ago (2016-12-20) | ||
Nmap (Network Mapper) is a security scanner, originally written by Gordon Lyon (also known by his pseudonym Fyodor Vaskovich), used to discover hosts and services on a computer network, thus building a "map" of the network. To accomplish its goal, Nmap sends specially crafted packets to the target host(s) and then analyzes the responses.
Contents
- Features
- Graphical interfaces
- Reporting results
- History
- Ethical issues and legality
- In popular culture
- In academia
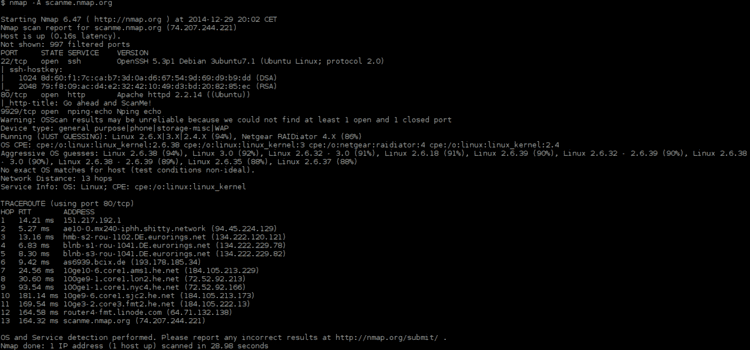
- Sample output
- References
The software provides a number of features for probing computer networks, including host discovery and service and operating-system detection. These features are extensible by scripts that provide more advanced service detection, vulnerability detection, and other features. Nmap can adapt to network conditions including latency and congestion during a scan. The Nmap user community continues to develop and refine the tool.
Nmap started as a Linux-only utility, but porting to Windows, Solaris, HP-UX, BSD variants (including OS X), AmigaOS, and IRIX have followed. Linux is the most popular platform, followed closely by Windows.
Features
Nmap features include:
Nmap can provide further information on targets, including reverse DNS names, device types, and MAC addresses.
Typical uses of Nmap:
Graphical interfaces
NmapFE, originally written by Zach Smith, was Nmap's official GUI for Nmap versions 2.2 to 4.22. For Nmap 4.50 (originally in the 4.22SOC development series) NmapFE was replaced with Zenmap, a new official graphical user interface based on UMIT, developed by Adriano Monteiro Marques.
Various web-based interfaces allow controlling Nmap or analysing Nmap results from a web browser. These include LOCALSCAN, nmap-web, Nmap-CGI, and IVRE.
Microsoft Windows specific GUIs exist, including NMapWin, which has not been updated since June 2003 (v1.4.0), and NMapW by Syhunt.
Reporting results
Nmap provides four possible output formats. All but the interactive output is saved to a file. Nmap output can be manipulated by text processing software, enabling the user to create customized reports.
History
Nmap was first published in September 1997, as an article in Phrack Magazine with source-code included. With help and contributions of the computer security community, development continued. Enhancements included operating system fingerprinting, service fingerprinting, code rewrites (C to C++), additional scan types, protocol support (e.g. IPv6, SCTP) and new programs that complement Nmap's core features. Changes include:
The Nmap Changelog records all changes.
Ethical issues and legality
Nmap is a tool that can be used to discover services running on Internet connected systems. Like any tool it could potentially be used for black hat hacking, as a precursor to attempts to gain unauthorized access to computer systems. Nmap is more often used by security and systems administration to assess networks for vulnerabilities.
System administrators can use Nmap to search for unauthorized servers, or for computers that do not conform to security standards.
Nmap is related to vulnerability assessment tools such as Nessus, which test for common vulnerabilities in open ports. The included NSE scripts that are packaged with modern versions of Nmap are able to perform vulnerability checks against discovered services.
In some jurisdictions, unauthorized port scanning is illegal.
In popular culture
In The Matrix Reloaded, Trinity is seen using Nmap to access a power plant's computer system, allowing Neo to "physically" break in to a building. The appearance of Nmap in the film was widely discussed on Internet forums and hailed as an unusually realistic example of hacking.
Nmap and NmapFE were used in The Listening, a 2006 movie about a former NSA officer who defects and mounts a clandestine counter-listening station high in the Italian alps.
Nmap source code can be seen in the movie Battle Royale, as well as brief views of the command line version of Nmap executing in Live Free or Die Hard and Bourne Ultimatum. In 2013, Nmap continued to make appearances in movies including popular sci-fi movie Elysium.
The film Dredd, a film adaptation of the famous Judge Dredd comics, was released in 2012 and also contains multiple Nmap scenes. Nmap is used for network reconnaissance and exploitation of the slum tower network. It is even seen briefly in the movie's trailer.
The command Nmap is widely used in the video game Hacknet, allowing to probe the network ports of a target system to hack it.
In academia
Nmap is an integral part of academic activities. It has been used for research involving the TCP/IP protocol suite and networking in general. As well as being a research tool, Nmap has become a research topic.
