 | ||
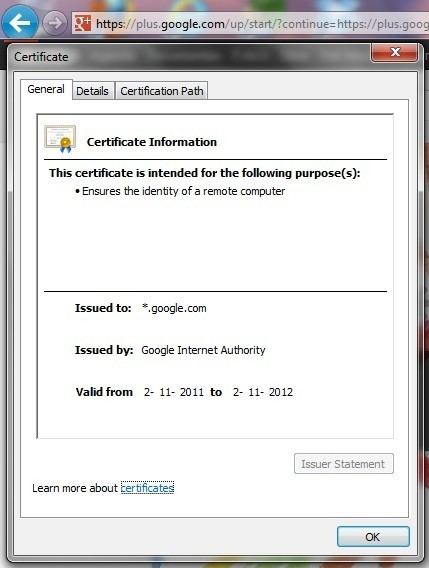
In computer networking, a wildcard certificate is a public key certificate which can be used with multiple subdomains of a domain. The principal use is for securing web sites with HTTPS, but there are also applications in many other fields. Compared with conventional certificates, a wildcard certificate can be cheaper and more convenient than a certificate for each domain.
Contents
Example
A single wildcard certificate for *.example.com, will secure all these domains:
Instead of getting separate certificates for sub domains, you can use a single certificate for all main domains and sub domains and save your money.
Because the wildcard only covers one level of subdomains (the asterisk doesn't match full stops), these domains would not be valid for the certificate:
The "naked" domain is valid when added separately as a Subject Alternative Name (SubjectAltName):
Note possible exceptions by CAs, for example wildcard Plus cert by DigiCert contains an automatic "Plus" property for the naked domain example.com
Limitation
Only a single level of subdomain matching is supported.
It is not possible to get a wildcard for an Extended Validation Certificate. A workaround could be to add every virtual host name in the Subject Alternative Name (SAN) extension, the major problem being that the certificate needs to be reissued whenever a new virtual server is added.
Wildcards can be added as domains in multi-domain certificates or Unified Communications Certificates (UCC). In addition, wildcards themselves can have subjectAltName extensions, including other wildcards. For example: The wildcard certificate *.wikipedia.org has *.m.wikimedia.org as a Subject Alternative Name. Thus it secures https://www.wikipedia.org as well as the completely different website name https://meta.m.wikimedia.org.
RFC 6125 argues against wildcard certificates on security grounds.
