Development status Active | ||
 | ||
Initial release June 22, 2013; 3 years ago (2013-06-22) Stable release 1.19 (October 17, 2016; 5 months ago (2016-10-17)) [±] Repository veracrypt.codeplex.com/SourceControl/latest | ||
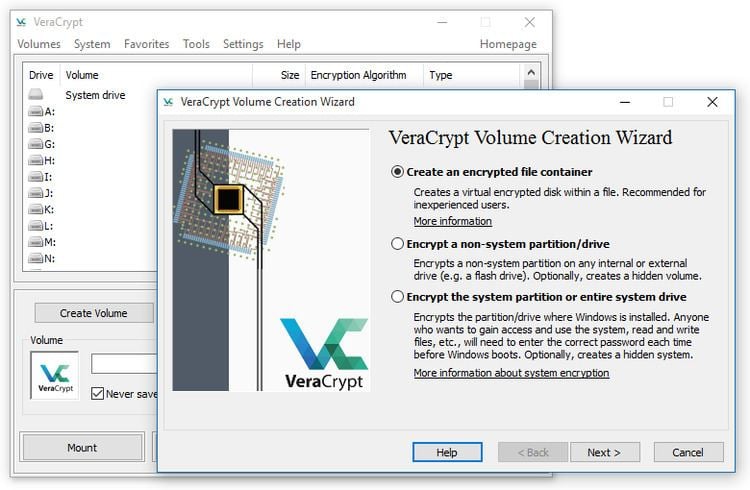
VeraCrypt is an open-source utility used for on-the-fly encryption (OTFE). It can create a virtual encrypted disk within a file or encrypt a partition or (in Windows) the entire storage device with pre-boot authentication.
Contents
- License and source model
- Algorithms
- Modes of operation
- Keys
- Plausible deniability
- Performance
- Security improvements
- Veracrypt audit
- Security precautions
- Encryption keys stored in memory
- Physical security
- Malware
- Trusted Platform Module
- Planned features
- References
VeraCrypt is a fork of the discontinued TrueCrypt project. It was initially released on June 22, 2013 and has produced its fourteenth release (version 1.19) as of October 17, 2016. Many security improvements have been implemented and issues raised by TrueCrypt code audits have been fixed (see below).
License and source model
VeraCrypt has been licensed under the Apache License 2.0 since 28 June 2015. Prior to that, it was released under the Microsoft Public License. VeraCrypt inherited a substantial amount of code from its TrueCrypt predecessor and thus is also subject to the terms of version 3.0 of the "TrueCrypt License" which is unique to the TrueCrypt software. It is not one of many widely used open-source licenses and is not a free software license according to the Free Software Foundation (FSF) license list, as it contains distribution and copyright-liability restrictions.
Algorithms
Individual ciphers supported by VeraCrypt are AES, Serpent, Twofish, Camellia, and Kuznyechik. The Magma cipher was removed in version 1.19 in response to a security audit. Additionally, five different combinations of cascaded algorithms are available: AES-Twofish, AES-Twofish-Serpent, Serpent-AES, Serpent-Twofish-AES and Twofish-Serpent. The cryptographic hash functions available for use in VeraCrypt are RIPEMD-160, SHA-256, SHA-512, Streebog and Whirlpool.
Modes of operation
VeraCrypt uses the XTS mode of operation.
Keys
The header key and the secondary header key (XTS mode) are generated using PBKDF2 with a 512-bit salt and 327,661 to 655,331 iterations, depending on the underlying hash function used.
Plausible deniability
As with its predecessor TrueCrypt, VeraCrypt supports plausible deniability by allowing a single "hidden volume" to be created within another volume. In addition, the Windows versions of VeraCrypt have the ability to create and run a hidden encrypted operating system whose existence may be denied.
The VeraCrypt documentation lists many ways in which VeraCrypt's hidden volume deniability features may be compromised (e.g. by third-party software which may leak information through temporary files, thumbnails, etc., to unencrypted disks) and possible ways to avoid this.
Performance
VeraCrypt supports parallelized encryption for multi-core systems and, under Microsoft Windows, pipelined read and write operations (a form of asynchronous processing) to reduce the performance hit of encryption and decryption. On newer processors supporting the AES-NI instruction set, VeraCrypt supports hardware-accelerated AES to further improve performance.
Security improvements
The VeraCrypt development team considered the TrueCrypt storage format too vulnerable to a National Security Agency (NSA) attack, so it created a new format incompatible with that of TrueCrypt. This is one of the main differences between VeraCrypt and its competitor CipherShed, which continues to use the TrueCrypt format. VeraCrypt is still capable of opening and converting volumes in the TrueCrypt format.
While TrueCrypt uses 1000 iterations of the PBKDF2-RIPEMD160 algorithm for system partitions, VeraCrypt uses 327,661 iterations. For standard containers and other partitions, VeraCrypt uses 655,331 iterations of RIPEMD160 and 500,000 iterations of SHA-2 and Whirlpool. While this makes VeraCrypt slower at opening encrypted partitions, it also makes password guessing attacks slower.
A vulnerability in the bootloader was fixed on Windows and various optimizations were made as well. The developers added support for SHA-256 to the system boot encryption option and also fixed a ShellExecute security issue. Linux and macOS users benefit from support for hard drives with sector sizes larger than 512. Linux also received support for the NTFS formatting of volumes.
VeraCrypt added the capability to encrypt GPT System Partitions and boot them using UEFI in version 1.18a.
An independent security audit of TrueCrypt released 29 September 2015 found TrueCrypt includes two vulnerabilities in the Windows installation driver allowing an attacker arbitrary code execution and privilege escalation via DLL hijacking. This was fixed in VeraCrypt in January 2016.
Veracrypt audit
An audit of VeraCrypt 1.18 was conducted by QuarksLab on behalf of the Open Source Technology Improvement Fund, taking 32 man-days and published on 17 October 2016. The major vulnerabilities identified in this audit were resolved in VeraCrypt 1.19, released the same day.
Security precautions
There are several kinds of attacks that all software-based disk encryption is vulnerable to. As with TrueCrypt, the VeraCrypt documentation instructs users to follow various security precautions to mitigate these attacks, several of which are detailed below.
Encryption keys stored in memory
VeraCrypt stores its keys in the RAM; on an ordinary personal computer the DRAM will maintain its contents for several seconds after power is cut (or longer if the temperature is lowered). Even if there is some degradation in the memory contents, various algorithms can intelligently recover the keys. This method, known as a cold boot attack (which would apply in particular to a notebook computer obtained while in power-on, suspended, or screen-locked mode), has been successfully used to attack a file system protected by TrueCrypt.
Physical security
VeraCrypt documentation states that VeraCrypt is unable to secure data on a computer if an attacker physically accessed it and VeraCrypt is then used on the compromised computer by the user again. This does not affect the common case of a stolen, lost, or confiscated computer. The attacker having physical access to a computer can, for example, install a hardware or a software keylogger, a bus-mastering device capturing memory or install any other malicious hardware or software, allowing the attacker to capture unencrypted data (including encryption keys and passwords) or to decrypt encrypted data using captured passwords or encryption keys. Therefore, physical security is a basic premise of a secure system. Attacks such as this are often called "evil maid attacks".
Malware
VeraCrypt documentation states that VeraCrypt cannot secure data on a computer if it has any kind of malware installed. Some kinds of malware are designed to log keystrokes, including typed passwords, that may then be sent to the attacker over the Internet or saved to an unencrypted local drive from which the attacker might be able to read it later, when they gain physical access to the computer.
Trusted Platform Module
The FAQ section of the VeraCrypt website states that the Trusted Platform Module (TPM) cannot be relied upon for security, because if the attacker has physical or administrative access to the computer and you use it afterwards, the computer could have been modified by the attacker e.g. a malicious component—such as a hardware keystroke logger—could have been used to capture the password or other sensitive information. Since the TPM does not prevent an attacker from maliciously modifying the computer, VeraCrypt will not support TPM.
Planned features
Unicode passwords are currently supported on Windows for all non-system encryption; future plans include providing Unicode capability throughout VeraCrypt.
