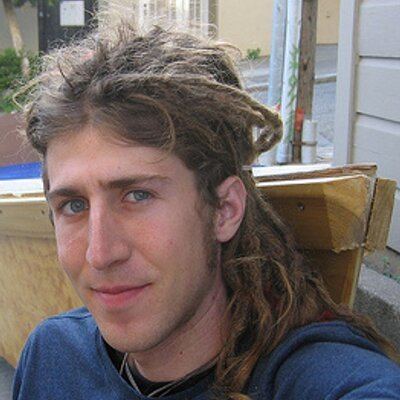
Citizenship US Name Moxie Marlinspike | Role Researcher | |
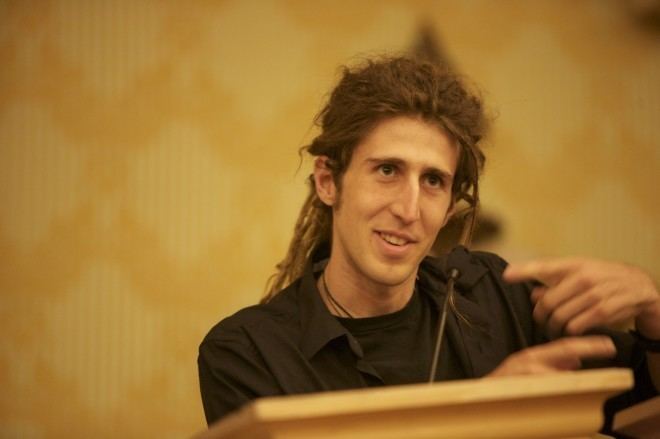 | ||
Other names Matthew Rosenfeld,Mike Benham Similar Dan Kaminsky, Charlie Miller, Whitfield Diffie, Bruce Schneier, Jeff Moss Born 1980 (age 41) | ||
Famed software engineer hacker moxie marlinspike and lance ulanoff on cyber security
Moxie Marlinspike (pseudonym) is an American Computer security researcher and cypherpunk. His research has focused primarily on techniques for intercepting communication, as well as methods for strengthening communication infrastructure against interception. Marlinspike is the former head of the security team at Twitter and founder of Open Whisper Systems. He is the author of a proposed SSL authentication system replacement called Convergence, co-author of the Signal Protocol, and a fellow at the Institute for Disruptive Studies. He runs a cloud-based WPA cracking service and manages a targeted anonymity service called GoogleSharing.
Contents
- Famed software engineer hacker moxie marlinspike and lance ulanoff on cyber security
- Black hat dc 09 moxie marlinspike interview
- Biography
- SSL stripping
- SSL implementation attacks
- Solutions to the CA problem
- Cracking MS CHAPv2
- Traveling
- Speaking engagements
- Recognition
- References

Black hat dc 09 moxie marlinspike interview
Biography
Originally from the state of Georgia, Marlinspike moved to San Francisco in the late 1990s. He then worked for several technology companies, including enterprise infrastructure software maker BEA Systems Inc. During the mid-2000s, Marlinspike bought a derelict 27-foot Catalina sailboat and, along with three friends, refurbished it and sailed around the Bahamas while making a documentary about their journey called Hold Fast.

In 2010, Marlinspike was the chief technology officer and co-founder of Whisper Systems, an enterprise mobile security startup company. In May 2010, Whisper Systems launched TextSecure and RedPhone. These were applications that provided end-to-end encrypted SMS messaging and voice calling, respectively. The company was acquired by the social-media firm Twitter for an undisclosed amount in late 2011. The acquisition was done "primarily so that Mr. Marlinspike could help the then-startup improve its security". During his time as head of cybersecurity at Twitter, the firm made Whisper Systems' apps open source.
Marlinspike left Twitter in early 2013 and founded Open Whisper Systems as a collaborative open source project for the continued development of TextSecure and RedPhone. At the time, Marlinspike and Trevor Perrin started developing the Signal Protocol, an early version of which was first introduced in the TextSecure app in February 2014. In November 2015, Open Whisper Systems unified the TextSecure and RedPhone applications as Signal. Between 2014 and 2016, Marlinspike worked with WhatsApp, Facebook, and Google to integrate the Signal Protocol into their messaging services.
SSL stripping
In a 2009 paper, Marlinspike introduced the concept of SSL stripping, a man-in-the-middle attack in which a network attacker could prevent a web browser from upgrading to an SSL connection in a subtle way that would likely go unnoticed by a user. He also announced the release of a tool, sslstrip, which would automatically perform these types of man-in-the-middle attacks. The HTTP Strict Transport Security (HSTS) specification was subsequently developed to combat these attacks.
SSL implementation attacks
Marlinspike has discovered a number of different vulnerabilities in popular SSL implementations. Notably, Marlinspike published a 2002 paper on exploiting SSL/TLS implementations that did not correctly verify the X.509 v3 "BasicConstraints" extension in public key certificate chains. This allowed anyone with a valid CA-signed certificate for any domain name to create what appeared to be valid CA-signed certificates for any other domain. The vulnerable SSL/TLS implementations included the Microsoft CryptoAPI, making Internet Explorer and all other Windows software that relied on SSL/TLS connections vulnerable to a man-in-the-middle attack. In 2011, the same vulnerability was discovered to have remained present in the SSL/TLS implementation on Apple Inc.'s iOS. Also notably, Marlinspike presented a 2009 paper, where he introduced the concept of a null-prefix attack on SSL certificates. He revealed that all major SSL implementations failed to properly verify the Common Name value of a certificate, such that they could be tricked into accepting forged certificates by embedding null characters into the CN field.
Solutions to the CA problem
In 2011, Marlinspike presented a talk titled SSL And The Future Of Authenticity at the Black Hat security conference in Las Vegas. He outlined many of the current problems with certificate authorities, and announced the release of a software project called Convergence to replace Certificate Authorities. In 2012, Marlinspike and Trevor Perrin submitted an Internet Draft for TACK, which is designed to provide SSL certificate pinning and help solve the CA problem, to the IETF.
Cracking MS-CHAPv2
In 2012, Marlinspike and David Hulton presented research that makes it possible to reduce the security of MS-CHAPv2 handshakes to a single DES encryption. Hulton built hardware capable of cracking the remaining DES encryption in less than 24 hours, and the two made the hardware available for anyone to use as an Internet service.
Traveling
Marlinspike says that when flying within the United States he is unable to print his own boarding pass, is required to have airline ticketing agents make a phone call in order to issue one, and is subjected to secondary screening at TSA security checkpoints.
While entering the United States via a flight from the Dominican Republic in 2010, Marlinspike was detained for five hours; federal agents requested his passwords, and all his electronic devices were confiscated and then returned.
