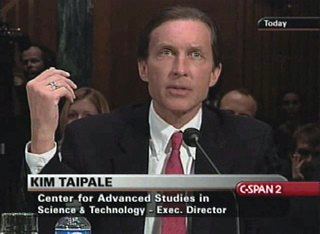
K. A. (Kim) Taipale is a lawyer, scholar, and social theorist specializing in information, technology, and national security policy. He is a partner in Stilwell Holding, a private investment firm, the founder and executive director of the Stilwell Center for Advanced Studies in Science and Technology Policy, a private, nonpartisan research organization, and a director of the Stilwell Charitable Fund. He was previously an investment banker at Lazard Freres & Co. and a lawyer at Davis Polk & Wardwell.
Taipale is a senior fellow at the World Policy Institute and serves on the Markle Foundation Task Force on National Security in the Information Age, and previously served on the Science and Engineering for National Security Advisory Board of the Heritage Foundation, the LexisNexis Information Policy Forum; and the Steering Committee of the American Law Institute's digital information privacy project. In addition, he has served on several corporate and non-profit boards.
Taipale is a frequent speaker and has written extensively on the intersection of information and technology policy with national and global security interests. He has testified before Congressional and other national committees, including on issues relating to foreign intelligence surveillance, data mining, biometrics, and information warfare. Taipale is a nationally recognized expert on technology and security policy, and related issues, including privacy and civil liberties. He is regularly quoted in the media, and has appeared frequently on PBS and NPR.
Taipale received a BA and JD from New York University and an MA, EdM, and LLM from Columbia University.
Introduction to Civil Liberties and Other Legal Issues, in The McGraw-Hill Homeland Security Handbook 2nd Edition (David Kamien, ed., McGraw-Hill, 2012) (ISBN 0071790845).Cyber-Deterrence, in Law, Policy and Technology: Cyberterorrism, Information Warfare, and Internet Immobilization (IGI Global 2011) (ISBN 1615208313).Power to the Edge: New Threats, New Responses, in America's Security Role in a Changing World: A Global Strategic Assessment 2009 (National Defense University 2009) (ISBN 0160832128).Why Can't We All Get Along? How Technology, Security and Privacy Can Co-exist in a Digital World, in Cybercrime and Digital Law Enforcement, Ex Machina: Law, Technology & Society Book Series, (Jack Balkin, et al., eds., NYU Press, 2007) (ISBN 0814799833).Designing Technical Systems to Support Policy: Enterprise Architecture, Policy Appliances, and Civil Liberties, in Emergent Information Technologies and Enabling Policies for Counter Terrorism (Robert Popp and John Yen, eds., Wiley-IEEE, 2006) (ISBN 0471776157).Seeking Symmetry in Fourth Generation Warfare: Information Operations in the War of Ideas, in Proceedings from Challenges in the Struggle Against Violent Extremism: Winning the War of Ideas (INSCT-Bantle 2006).Introduction to Domestic Security and Civil Liberties, in The McGraw-Hill Homeland Security Handbook (David Kamien, ed., McGraw-Hill, 2005) (ISBN 0071446656).Journal articles and papers
Identity and Resilience, Paul Trevithick, William Coleman, John Clippinger, and Kim Taipale (White House Cyberspace Policy Review Document 2009).Seeking Symmetry on the Information Front: Confronting Global Jihad on the Internet, 16 Nat'l Strategy F. Rev. 14 (Summer 2007).The Ear of Dionysus: Rethinking Foreign Intelligence Surveillance, 9 Yale J. L. & Tech. 128 (Spring 2007).Rethinking Foreign Intelligence Surveillance, World Policy Journal, Vol. XIII (Winter 2006-2007).Whispering Wires and Warrantless Wiretaps: Data Mining and Foreign Intelligence Surveillance, N.Y.U. Rev. L. & Security, No. VII Supl. Bull. on L. & Sec.: The NSA and the War on Terror (Spring 2006).The Trusted Systems Problem: Security Envelopes, Statistical Threat Analysis, and the Presumption of Innocence, IEEE Intelligent Systems, Vol. 20 No. 5, (Sept./Oct. 2005).Technology, Security and Privacy: The Fear of Frankenstein, the Mythology of Privacy, and the Lessons of King Ludd, 7 Yale J. L. & Tech. 123; 9 Intl. J. Comm. L. & Pol'y 8 (Dec. 2004).Data Mining and Domestic Security: Connecting the Dots to Make Sense of Data, 5 Colum. Sci. & Tech. L. Rev. 2 (Dec. 2003).Managing Digital Assets: The Challenge of Creating and Sustaining Intangible Value in a Data-Driven Economy, David Bollier, rapp. (Aspen Institute 2015) (ISBN 0898436168).POWER-CURVE SOCIETY: The Future of Innovation, Opportunity and Social Equity in the Emerging Networked Economy, David Bollier, rapp. (Aspen Institute 2013) (ISBN 0-89843-582-X).The Future of Work: What It Means for Individuals, Businesses, Markets and Governments, David Bollier, rapp. (Aspen Institute 2011) (ISBN 0898435439).The Promise and Peril of Big Data, David Bollier, rapp. (Aspen Institute 2010) (ISBN 0898435161).No More Secrets: National Security Strategies for a Transparent World, S. E. Spaulding, conv., A. Kochems, rapp. (ABA-SCLNS, Off. of the Nat'l Counterintelligence Exec., & Nat'l Strategy F. 2010).Biometric Recognition: Challenges and Opportunities, J. N. Pato and L. I. Millett, eds. (National Academies Press 2010) (ISBN 0309142083).Identity in the Age of Cloud Computing, J.D. Lasica, rapp. (Aspen Institute 2009) (ISBN 0898435056).Technology, Policy, Law, and Ethics Regarding U.S. Acquisition and Use of Cyberattack Capabilities, W. A. Owens, K. W. Dam, and H. S. Lin, eds. (National Academies Press 2009) (ISBN 0309138507).Protecting Individual Privacy in the Struggle Against Terrorist, Committee on Technical and Privacy Dimensions of Information for Terrorism Prevention and Other National Goals (National Academies Press 2008) (ISBN 0309124883).Mobilizing Information to Prevent Terrorism, Third Report of the Markle Foundation Task Force on National Security in the Information Age, Zoe Baird & James Barksdale, chmn. (Jul. 2006).Implementing a Trusted Information Sharing Environment, Markle Foundation Task Force on National Security in the Information Age, Zoe Baird & James Barksdale, chmn. ( Feb. 2006).Commentary, Security vs. Privacy: Security, The Huffington Post (Nov. 9, 2007).Commentary (with James Jay Carafano), Free the Hostages: Continuing FISA Concerns, National Review Online (Oct. 24, 2007).New Authority to Oversight Foreign Intelligence Needed, Program on Law Enforcement and National Security in the Information Age, World Policy Institute (May 7, 2007).FISA Should be Amended, Says Center for Advanced Studies, Program on Law Enforcement and National Security in the Information Age, World Policy Institute (Apr. 19, 2007).Is Net Neutrality Bad for National Preparedness?, Program on Telecommunications and Cybersecurity Policy, World Policy Institute (Jun. 14, 2006).Commentary (with James Jay Carafano), Fixing Foreign Intelligence Surveillance, The Washington Times (Jan. 24, 2006).Not Issuing Driver's Licenses to Illegal Aliens is Bad for National Security, Program on Law Enforcement and National Security in the Information Age, World Policy Institute (Dec. 17, 2004).Government Should Not Rush to Massive ID Surveillance System, Global Information Society Project, World Policy Institute (Oct. 29, 2004).