 | ||
A general protection fault (GPF) in the Intel x86 and AMD x86-64 types of computer microprocessor architectures, and other unrelated architectures, is a fault (a type of interrupt) that can encompass several cases in which protection mechanisms within the processor architecture are violated by any of the programs that are running, either the kernel or a user program. The mechanism is first described in section 9.8.13 in the Intel 80386 programmer's reference manual from 1986. A general protection fault is implemented as an interrupt (vector number 13 in decimal) in both the x86 and the AMD64 architectures.
Contents
- Behaviour in specific operating systems
- Memory errors
- Privilege errors
- Technical causes for faults
- Segment limits exceeded
- Segment permissions violated
- Segments illegally loaded
- Switching
- Miscellaneous
- References
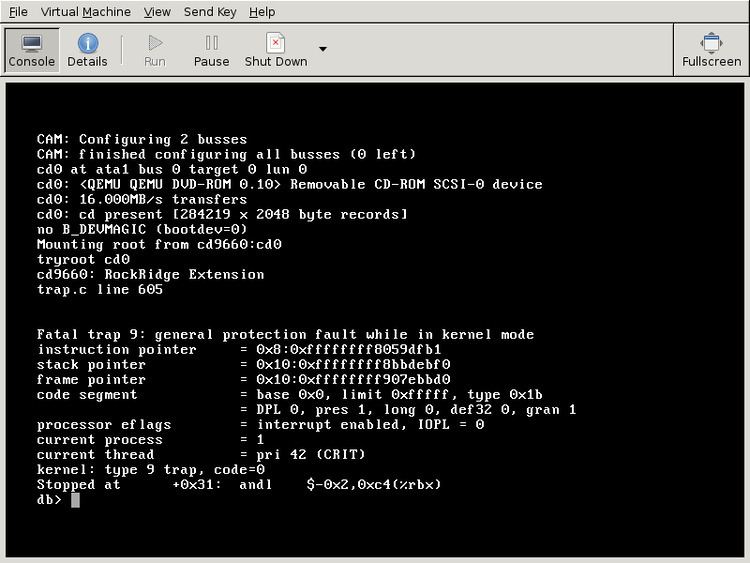
If the processor detects a protection violation, it stops executing the code and sends a GPF interrupt. In most cases the operating system removes the failing process from the execution queue, signals the user, and continues executing other processes. If, however, the operating system fails to catch the general protection fault, i.e. another protection violation occurs before the operating system returns from the previous GPF interrupt, the processor signals a double fault, stopping the operating system. If yet another failure (triple fault) occurs, the processor stops working and only responds to a reset.
Behaviour in specific operating systems
In Microsoft Windows, the general protection fault presents with varied language, depending on product version:
In systems such as Unix and Linux, the errors are reported separately (e.g. segmentation fault for memory errors).
Memory errors
In memory errors, the faulting program accesses memory that it should not access. Examples include:
However, many modern operating systems implement their memory access-control schemes via paging instead of segmentation, so it is often the case that invalid memory references in operating systems such as Windows are reported via page faults instead of general protection faults. Operating systems typically provide an abstraction layer (such as exception handling or signals) that hides whatever internal processor mechanism was used to raise a memory access error from a program, for the purposes of providing a standard interface for handling many different types of processor-generated error conditions.
In terms of the x86 architecture, general protection faults are specific to segmentation-based protection when it comes to memory accesses. However, general protection faults are still used to report other protection violations (aside from memory access violations) when paging is used, such as the use of instructions not accessible from the current privilege level (CPL).
While it is theoretically possible for an operating system to utilize both paging and segmentation, for the most part, common operating systems typically rely on paging for the bulk of their memory access control needs.
Privilege errors
There are some things on a computer which are reserved for the exclusive use of the operating system. If a program which is not part of the operating system attempts to use one of these features, it may cause a general protection fault.
Additionally, there are storage locations which are reserved both for the operating system and the processor itself. As a consequence of their reservation, they are read-only and an attempt to write data to them by an unprivileged program is an error.
Technical causes for faults
General protection faults are raised by the processor when a protected instruction is encountered which exceeds the permission level of the currently executing task, either because a user-mode program is attempting a protected instruction, or because the operating system has issued a request which would put the processor into an undefined state.
General protection faults are caught and handled by modern operating systems. Generally, if the fault originated in a user-mode program, the user-mode program is terminated. If, however, the fault originated in a core system driver or the operating system itself, the operating system usually saves diagnostic information either to a file or to the screen and stops operating. It either restarts the computer or displays an error screen, such as a Blue Screen of Death or kernel panic.
Segment limits exceeded
Segment limits can be exceeded:
Segment permissions violated
Segment permissions can be violated by:
Segments illegally loaded
This can occur when:
Switching
Faults can occur in the task state segment (TSS) structure when:
Miscellaneous
Other causes of general protection faults are:
