Name The Jester Role Hacktivist | ||
 | ||
Known for Hacking Anti-American, jihadist, and homophobic websites Website | ||
The Jester (also known by the leetspeak handle th3j35t3r) is an unidentified computer vigilante who describes himself as a grey hat hacktivist. He claims to be responsible for attacks on WikiLeaks, 4chan, Iranian President Mahmoud Ahmadinejad, and Islamist websites. He claims to be acting out of American patriotism. The Jester uses a denial-of-service (DoS) tool known as "XerXeS", that he claims to have developed. One of The Jester's habits is to tweet "TANGO DOWN" on Twitter whenever he purports to have successfully taken down a website.
Contents
- Identity and communication
- Military service
- XerXeS and other tools
- Hacking history
- SANS report The Jester A Lesson in Asymmetric Warfare
- QR code attack
- References
Identity and communication

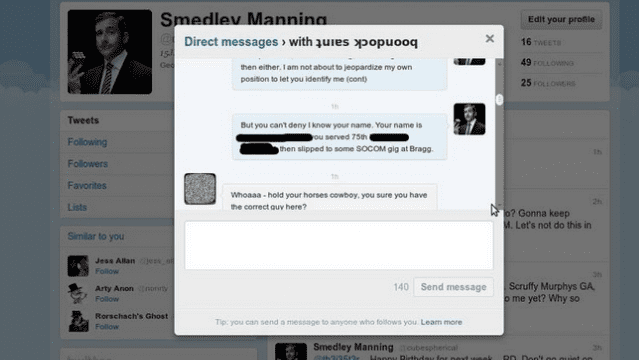
The Jester first appeared on Twitter, where he announced his attack on the Taliban website alemarah.info on January 1, 2010. On June 26, 2010, he established his WordPress blog "Jester's Court". The Jester also communicates via his I2P IRC channel #jester and cautions these are the only three authentic methods of communication from him: "As per usual, because of the large amount of imposters trying to pass themselves off as me I will only speak in THREE places, here via this blog, my twitter and the i2p IRC network outlined above where my nick (th3j35t3r) is registered to myself. If you see a ‘jester’ anywhere else it’s not me."
Military service
The Jester had stated that he was a former soldier and had served in Afghanistan and elsewhere. A former defense operative claimed that The Jester was a former military contractor involved in US Special Operations Command projects. On April 10, 2012, The Jester gave a live chat interview to a class of Computer Science students at the University of Southern Maine where he confirmed his military service and stated he served four "operational tours".
XerXeS and other tools
The Jester claims to have originally developed his DoS script as a means to test and harden servers. After learning from an article that Jihadists were using the Internet to recruit and coordinate terror cells, The Jester resolved to disrupt online communications between Jihadists. He weaponized his script and created a front-end known as "XerXeS" in order to solve the script's usability problems.
Hacking history

On January 1, 2010, The Jester began a campaign against Jihadist websites. His first target was alemarah.info, which was the Taliban's website at the time.
On November 28, 2010, The Jester posted several tweets claiming to be responsible for the downtime WikiLeaks was experiencing. He justified his alleged attacks by claiming that WikiLeaks was "attempting to endanger the lives of our [US] troops, 'other assets' & foreign relations." In retaliation to The Jester's reported efforts, hacktivists including a group named Anonymous in support of WikiLeaks were reported as temporarily disrupting the website of MasterCard as well as attacking websites of Amazon and PayPal.
On November 29, 2010, someone claiming to be The Jester stated that he had been raided by the U.S. and attempted to solicit money for legal fees. The Jester purported that the person was an impostor, though writers at InfoSecIsland believe the hoax was created by The Jester himself.
On December 28, 2010, a DoS attack targeted 4chan.org. On that same day, The Jester tweeted "4chan.org — that looks like a TANGO DOWN (not) maybe you guys pissed off the wrong person trying to (wrongly) ID me?" This tweet is believed to be a reference to claims by 4chan users that The Jester was a man from Montana.
On February 21, 2011, The Jester began a DoS attack on several sites belonging to the Westboro Baptist Church for celebrating the death of homosexual U.S. service men.
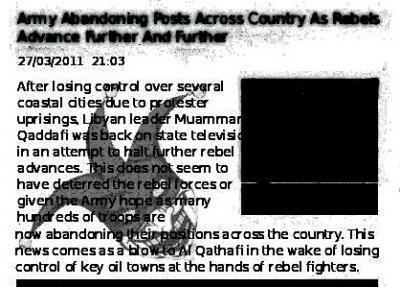
In March 2011, The Jester employed a different style of attack by using an XSS vulnerability to make it appear as if fabricated articles were inserted online Libyan newspapers The Malta Independent Online and the Tripoli Post. On March 28, 2011, he tweeted links to the forged articles. The articles were not visible in search, or to viewers of those websites, and viewable only via the inserted links. These tweets drew the attention of Anthony M. Freed, who examined the articles and discovered they were anomalies not contained in the newspapers' respective archives. Further inspection by Freed revealed The Jester left a watermark of his signature Harlequin avatar on the articles he created, which can only be seen by tilting the computer monitor back at an angle. The fabricated articles reported degradation in troop morale among fighters loyal to Muammar Gaddafi and incidents of his soldiers abandoning their posts. Freed concluded The Jester's objective was a "psyops campaign aimed at breaking the spirit of the troops loyal to Libyan strongman Muammar Gaddafi." The Jester confirmed this in a subsequent interview later the same year.
In June 2011 The Jester vowed to find and expose members of LulzSec. He attempted to obtain and publish personally identifiable information of key members within group, whom he described as "childish". On June 24, 2011, he claimed to have revealed the identity of LulzSec leader Sabu as Xavier Kaotico, an information technology consultant possibly from New York City. In July of the same year he falsely accused Hugo Carvalho, a Portuguese IT professional, of also being Sabu, leaving The Jester's outing claims to be considered suspect. However, in a post on his blog in November 2011, The Jester retracted his prior identifications for "Sabu", issued an apology and correctly identified "Sabu" as Hector Xavier Monsegur, 28, of New York. Sabu's identity was confirmed on March 6, 2012, when Monsegur was arrested by the FBI and it was revealed that he had been acting as an FBI informant in the interim.
In October 2011, at the Hackers Halted USA conference, The Jester gave a surprise live presentation and fielded questions through an online chat with presenter Jeff Bardin. His identity was authenticated via his Twitter account. Jester answered questions about XerXeS and other tools in development, and discussed his motivations for attacking militant jihadi recruiting websites. On August 26, 2012, Bardin hosted a similar presentation at Utica College for the college's Cybersecurity Master's program.
Late November 2011, th3j35t3r claimed to take down multiple jihadist sites permanently, with his newest tool known as 'Saladin'. Saladin is claimed to be similar to other 'Apache Killer' tools used by hackers. Critics have claimed Saladin does not exist, and that he is relying on domain expiration.
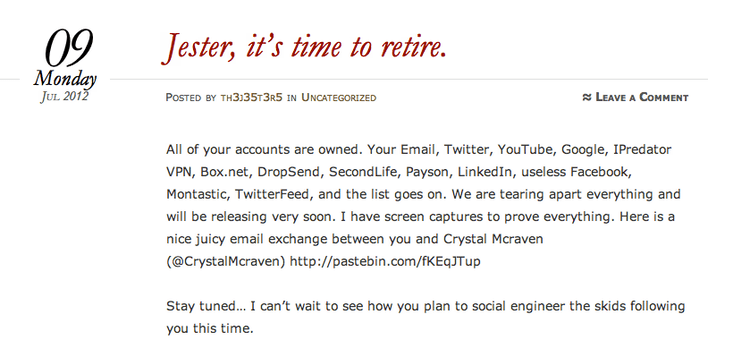
On May 14, 2012 The Jester's Twitter account (@th3j35t3r) appeared to have been deleted, along with all posts on his WordPress blog. However, the Twitter account and WordPress blog were merely temporarily deactivated and were subsequently restored May 16, 2012.
On July 2, 2013, the Jester took responsibility for a series of DoS cyberattacks against the Ecuadorean stock exchange and the country's tourism website, and promised to attack any other governments considering granting asylum to NSA leaker Edward Snowden. In a June blog post, he wrote that Snowden "is not a goddam hero, here to save Americans from 'the government' because of privacy infringements and breaches of the 4th amendment, he is a traitor and has jeopardized all our lives." In tweets, the Jester also alluded to a plan to seize control of the fire alarms at the Ecuadorean embassy in London, which would force WikiLeaks founder Julian Assange to set foot on UK soil and face potential extradition to Sweden to face sexual assault charges.
On October 21, 2016, the Jester took responsibility for defacing the official website of the Russian Ministry of Foreign Affairs. The "hack" was in retaliation for a series of DDOS attacks earlier in the week that targeted major DNS provider Dyn.
SANS report: "The Jester: A Lesson in Asymmetric Warfare"
In December 2011, T. J. O'Connor, a research analyst in the Information Technology and Operations Center (ITOC), produced a comprehensive report for the SANS Institute detailing the history of The Jester's hacking campaigns titled "The Jester Dynamic: A Lesson in Asymmetric Unmanaged Cyber Warfare". The paper examines the history, motives and impact of two years worth of The Jester's hacking, and provides a detailed analysis of the timeline of his attacks, a speculative analysis of the tools he may use, and review of his use of social media and public relations through his blog.
QR code attack
On March 5, 2012, The Jester changed his Twitter account @th3j35t3r avatar from his signature Jester icon to a QR code without comment or explanation. Scanning a QR code redirects a browser to a website. Scanning The Jester's icon led to a URL where he had an image of his signature Jester icon and an embedded, hidden code that allegedly exploited a vulnerability that affects Safari, Chrome and Android browsers. "When anyone scanned the original QR code using an iPhone or Android device, their device would silently make a TCP shell connection back to my remote server," The Jester wrote. "Like a phone call, if you like."
Apparently, once connected to the Jester's server, the network diagnostic tool Netcat checked the connecting mobile device to see if it had Twitter software installed. Twitter account information was then harvested and checked against a list that The Jester allegedly maintains of known Twitter accounts associated with the hacking groups Anonymous, LulzSec or AntiSec, with Wikileaks, Al Qaeda and Islamic Jihadi recruiting sites. Twitter accounts that did not hit a match to the list were ignored. Possibly, when a Twitter account registered a hit on the list, the account permissions were transferred to The Jester, he elevated his permissions to allow him to exploit the entire mobile device. It is possible that in this manner The Jester was able to obtain access to SMS text messages, voicemail, call logs, and email on the phone.
The Jester's QR code ran quietly for five days before a Twitter user going by the moniker @RootDial noticed the embedded code and mentioned it. In those five days, The Jester wrote "Over 1,200 curious netizens scanned the QR code . . . Of those, over 500 devices reverse-shelled back to the listening server. Of those, a significant number were on the '[hit]-list' and as such treated as valid targets."
On March 12, The Jester posted an encrypted file containing the data harvested from his QR code. In a private communication, SecurityNewsDaily asked The Jester why he'd encrypted the information rather than post it in regular, plain text. "I encrypt my [data] dumps as a matter of course because I am not the same as my detractors who drop personal info all the time," he replied. "The right people have the plain text dump. It would be highly irresponsible of me to be dropping anything in the open."
